IC Data Communications LLC Blog
One month ago, the United States Federal Communications Commission put forth a ban on the sale of all Wi-Fi routers made outside the US, giving manufacturers the option to apply for a conditional approval exemption on the agency’s website.
Let’s talk about what this ban is going to mean to your business (and to your entire team’s personal lives) as things progress. Fair warning, things aren’t going to be simple.
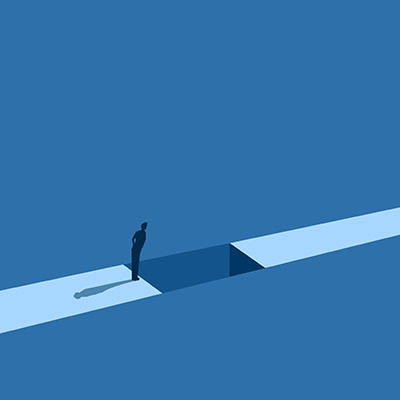
For decades, the cybersecurity industry has operated on a comfortable, if flawed, assumption: finding a Zero-Day vulnerability (a bug unknown to the developers) was a Herculean task. It required elite human developers and ethical hackers, months of manual code review, and high-cost developer tools. This friction gave defenders a grace period—a window of time where obscurity acted as a shield.
That era officially ended on April 6, 2026.
Many business owners look at their monthly IT expenses as a necessary evil, or even a sunk cost, like an electric bill or an office lease. You pay for it because you have to, not because it promises to help you win over new clients or unlock new opportunities. This is the mindset that’s going to get you left in the dust by your competitors, and if you’re still thinking about IT this way, you need to change your mind, and fast.
A small business is a complex machine, even in its simplest form. One cog that’s not operating at the appropriate capacity can create operational problems that lead to bigger, more expensive issues later down the road. While businesses worry about the economy and ensuing financial issues, the reality is that your business is far more likely to fail due to operational inefficiencies.
Are you sick of switching between windows countless times to get the right information from one place to another? Not only is this pattern annoying, but it also wastes valuable time and welcomes errors.
However, Windows 11’s clipboard feature includes Clipboard History, which largely eliminates this issue. Let’s talk about what it is, what it can do, and—critically—how you can use it.
Imagine the terror of arriving at the office only to find every screen glowing with the same cryptic message: "Your files are encrypted." If you’re like most business owners, this kind of situation could set you back weeks, and that’s not to mention the financial setback and permanent data loss that could occur as a result of such a ransomware attack. What your business needs is resilience, the kind that only immutable backups can offer.
What do you do when you realize you’ve written three sentences of absolute nonsense?
What do most of us do? We lean on the Backspace key. We sit there, staring at the screen, watching the cursor slowly eat away at the alphabet like Pac-Man. Waka-waka-waka-waka. The funny thing is that all that holding down the backspace key for five seconds is inefficient, and quite frankly, you’re better than that. It’s time to stop making a fool out of yourself and start tactically deleting your text. Let’s teach you how:
We’ve all been there. A client walks into the office, a contractor needs to check a manual, or a visitor is waiting in the lobby, and they ask that ubiquitous question: "What’s the Wi-Fi password?"
Sharing it feels like common courtesy, of course. If you are handing them the password to your primary office network, you are doing much more than sharing an internet connection. You are essentially handing a stranger the keys to your entire digital office.
The Federal Trade Commission has spent years providing businesses with guidance and advice concerning their security. Now, this guidance has converted into enforceable mandates.
In short, your business needs to have systems and protections in place—not plans—in order to abide by last month’s executive order that focuses on the prevention of cybercrime and fraud. Let’s touch on what needs to be accomplished in order for you to do so.
Do you look at your technology as a cost center to be managed, or as a springboard for new revenue? If you’ve been following us for a while, you know we like to think of it as the latter. Small businesses spend much of their IT budget just to keep the lights on, stuck in an endless cycle of “surviving” rather than “thriving.” But with a virtual CIO, or vCIO, your business can reframe the conversation surrounding technology and look at it as an endless realm of opportunity rather than an endless loop of costs.
I’d be willing to wager that one of any small or even medium-sized business’ biggest (or at least most frustrating) challenges is scheduling. Of course, you want your workforce to be running at full capacity as much as possible, but Jack requested a half day to see his daughter’s piano recital on Thursday, and Stef’s life would be a lot easier if she had Thursday mornings free.
Fortunately, today’s tech makes dealing with all of this much easier, especially when paired with the right strategy for your business.
You’ve probably heard a lot of password advice over the past decade, but how much of it is actually good advice that you should listen to? These days, with advanced automated threats able to crack incredibly complex passwords with ease, you can’t be too careful. You might even need to take a different approach entirely… which brings us to the OG password advice: just make it longer.
For years, the firewall was seen purely as a defensive tool—an all-in-one solution with antivirus, web filtering, and intrusion protection. Nowadays, they can potentially serve a much greater purpose beyond simple network security. When leveraged right, you can use the immense amount of data firewalls track to identify bottlenecks, optimize workflows, and make smarter infrastructure investments.
If your meetings feel like a lot is being said, but your goals are never really accomplished, you are in very good company. Approximately $37 billion USD is lost each and every year to unproductive meetings alone. When you consider how much of that $37 billion is potentially due to your business’ meetings, one could hardly blame you for being sick about it.
Let’s take a look at a few ways that you can make the most of the time you spend in meetings.
Are you under the impression that having a backup is the same thing as a successful recovery? These days, businesses think they are mutually exclusive, but the fact remains that having a backup synced to the cloud is not enough to keep your business running when the odds are against you. In fact, your files might be fine, but your business could be dead in the water due to ongoing downtime.
Forget the high-octane hacker montages you see in movies. Real cybercrime isn’t a smash-and-grab; it’s a slow-burn infiltration.
Most bad actors aren’t looking to make a scene—they’re looking to get comfortable. On average, an intruder spends six months lurking inside a network before they are ever detected. During this time, they are quietly harvesting data, mapping your systems, and waiting for the most profitable moment to strike.